If you have been paying attention to headlines over the last two years, then you should be fully aware of the increasing rate of cyberattacks impacting organizations across every sector, including government, technology, education, and healthcare, which unfortunately tends to be one of the most targeted sectors.
The reason for that is simple: healthcare organizations are typically very lucrative and handle a ton of high-value data, including patient records, proprietary information, and other sensitive personal health information (PHI) that can be stolen and leveraged.
 Stolen medical records can be sold on the dark web for as much as $1,000 per record, making PHI an enticing target for cyber criminals, especially if a large enough system can be compromised. We’re talking about large healthcare groups that hold records for millions of patients.
Stolen medical records can be sold on the dark web for as much as $1,000 per record, making PHI an enticing target for cyber criminals, especially if a large enough system can be compromised. We’re talking about large healthcare groups that hold records for millions of patients.
This is why healthcare organizations have the highest industry cost of a breach – $9.23 million per incident. This cost is up nearly 30% from 2020, according to IBM’s annual Cost of a Data Breach Report, which has listed healthcare as the costliest industry when it comes to mitigating cyberattacks – an accolade the sector has claimed for 11 consecutive years.
A NOTE ABOUT HACKERS
Hackers – whether affiliated with a nation state or other organized crime groups – are opportunistic. They take advantage and pounce when your attention is diverted, which is why cyberattacks have increased since the start of the pandemic. Some 70% of hospitals, surveyed last November, reported that they were the victim of a cyberattack within the last 12 months.
The healthcare industry has been one of the heaviest targeted sectors since the beginning of the pandemic and, shockingly, cybersecurity is still not a high priority for health group executives and overworked practice administrators. Only 40% of healthcare cybersecurity professionals surveyed in an early 2021 HIMSS survey expect budgets to receive appropriate funding over the next two to three years.
Coupled with the typical cybercrime model of exploiting world events, healthcare – much like every other sector – has increased its technology usage, creating an even greater opportunity for criminals to strike.
TOP CYBER ATTACKS, AND HOW TO AVOID THEM
Phishing
Phishing is one of the most known, and most successful, attack strategies in a cyber criminal’s arsenal. If you’ve ever been alerted by your email provider of a suspicious email that included a link or attachment, you’ve come face-to-face with a phishing email.
These emails are a social engineering trick designed to get you to click on a malicious link or attachment. When you do, malware is launched in your system. These attempts often look very legitimate and may appear to come from someone within your organization. The email may even appear to come from someone you’ve interacted with in the past.
U.S. agencies warned during the pandemic of fraudulent emails purporting to be from the U.S. Centers for Disease Control or other organizations claiming to offer COVID information. Others asked for charitable donations, information about financial relief, and details about vaccines and testing.
This was a clever strategy for cyber criminals because people were anxious and hungry for information regarding the virus. This resulted in high click volume, and many were infected with malware that gave criminals access to sensitive patient data, locked IT systems for ransom, and established a foothold in many IT environments.
To combat phishing attacks, follow these steps:
- Conduct regular training with staff on how to spot a phishing attack. End users are typically the weakest link when it comes to a cyberattack, and human error, like clicking on a malicious link in an email, is one of the main infection vectors. This training may include simulated phishing attacks to help you identify which users are a problem.
- Invest in email security and firewalls. Several email filtering tools exist that can help identify suspicious emails and isolate them before anyone even thinks about clicking on them, and firewalls will help identify threats.
- Keep web browsers and other software up to date. Tech companies routinely issue updates to patch security vulnerabilities, and hackers are usually quick to exploit those vulnerabilities once they’re identified along with the update. Waste no time in patching your systems.
- Implement multi-factor authentication. This technology adds another layer of security when logging into accounts by asking for a code or other form of authentication, such as a USB security key. Without that code (typically delivered via email, text, or an authentication app), an attacker won’t be unable to successfully log in.
Ransomware
One of the main reasons hackers conduct phishing attacks is to deploy ransomware, which locks a computer until the victim pays a ransom. Depending on the attacker’s abilities and the configuration of the victim’s network, the infection may spread throughout the entire organization and force a system-wide shutdown.
However, the ransom demand – which can stretch into the millions for a profitable healthcare organization – isn’t the only concern. Ransomware operators have been known to engage in double and triple extortion in which they threaten to release stolen records, taking the attack public if the ransom is not paid.
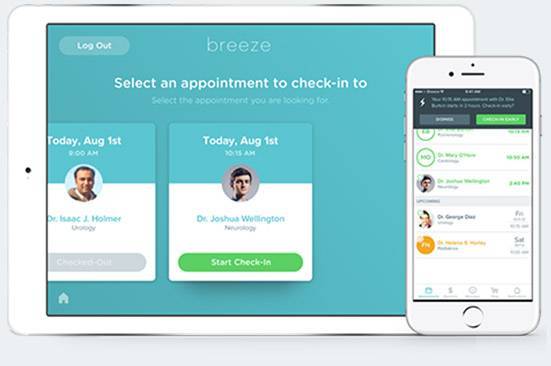
Secure Patient’s Data With Nordlabs:
Now, you can secure your patient’s data with Nordlabs platform, which provides innovative cybersecurity-focused solutions, preventing unauthorized access and potential breaches.
Studies of ransomware trends over the pandemic have found a dramatic increase in attacks, with an increase of nearly 300% during select quarters in 2021. Healthcare, of course, is one of the most targeted industries for ransomware, with some studies suggesting healthcare ransomware attacks have increased by 45% over the last 12 months. Recent cases include an October attack against Planned Parenthood Los Angeles, which notified about 400,000 patients that parts of their PHI were stolen. Meanwhile, several other healthcare systems have reported ransomware attacks impacting millions of patients, resulting in system downtime that further impacted critical services.
To avoid falling victim to a ransomware attack, we recommend the following (in addition to the steps listed above):
- Make sure systems are backed up offline. When a ransomware attack happens, the cheapest method of mitigation is usually to recover from a system backup. However, that backup must be stored offline to block the threat actor.
- Segment networks. If the attacker compromises systems on a non-critical network that has been segmented from the rest of the organization’s systems, then recovery will be much easier and there will be less of an impact on the rest of the organization.
- Patch systems immediately. While phishing and human error are the main entry points for ransomware, hackers also look for flaws in software that allow them to enter networks. Quickly patching those flaws and applying updates, as they become available, will help limit your organization’s exposure to attacks.
- Secure remote desktop protocol (RDP). Hackers can also gain access through exposed, poorly secured remote services. Look for systems using RDP, close unused RDP ports, and enforce account lockouts after a specified number of attempts.
- Create an incident response plan. A response plan is designed to give IT and other employees a roadmap for mitigating a ransomware attack.
Supply Chain attacks
These clever, hard-to-detect attacks leverage a trusted software or service provider to infect an organization.
In the SolarWinds incident, hackers believed to be affiliated with the Russian government first compromised a widely used IT management product from the company and inserted malware into an update. This gave the hackers unfettered access into thousands of organizations using the software, including some U.S. agencies. The Kaseya incident was a massive ransomware campaign that leveraged another popular IT management product to deploy ransomware via third-party IT services providers.
Microsoft calls these attacks an emerging threat in which attackers gain access to source codes, build processes or update mechanisms of IT vendors, and leverage the massive IT supply chain for distribution. Instead of targeting individual victims, attackers use this method to compromise thousands at the same time, giving them the ability to pick and choose which customer of the IT vendor to attack further.
These attacks are difficult to spot because these tools from trusted companies aren’t normally on an organization’s threat radar.
However, there are several recommended steps to prevent and mitigate these attacks:
- Be selective when choosing a software vendor. Before doing business with a services provider, ask for a software bill of materials (SBOM) that provides a detailed list of the components in the software product. This allows you to perform a vulnerability or license analysis. Partnering with a service and solution provider with a strong cybersecurity posture will help ease concerns.
- Monitor software for unusual activity. If the program is behaving in an unexpected way, it could be a sign that the tool is being used or of malicious activity present. If malicious activity is detected, disable the software, remote its access to the network, and notify the vendor. Engage your incident response plan and work with forensic teams to track down the extent of the compromise.
- Implement a Zero Trust network architecture. This approach goes beyond monitoring users and external threats. Each user is authenticated every step of the way, and nothing on the network is inherently trusted. This strategy includes multi-factor authentication on all systems, network micro-segmentation, endpoint detection and response tools, and more.
Conclusion
The modern hacker is no longer an amateur attacker operating out of a dark basement. Attacks are most often launched by complex, experienced groups that are well-organized. They are increasingly adopting business models similar to legitimate technology providers, which is contributing to a growing cybercrime market estimated to cost the world more than $10 trillion by 2025.
This is why it is critical that your organization invests in network defenses and partners with software providers who will work to keep your system and PHI secure. Ask yourself if you can afford to have systems offline for more than a few minutes. Think about the damage it will do to your patients, your revenues, and your organization’s reputation.